In the morning, one of your sales team tells you she can’t find the records on her deals. As you start to investigate, similar reports trickle in from others across the company. By lunchtime it’s clear that your org has seen significant data loss, and the metadata shaping your org has also been affected. Not only are records missing, the fields that hold those records aren’t there either. What would you do next?
A scenario like this is a real risk for Salesforce orgs, and your company needs to have a response prepared. Having a backup solution in place with backups of both data and metadata is absolutely essential. It’s also well worth creating or reviewing your own incident response plan. This post sets out the things that plan should contain for your Salesforce team.
The value of an incident response plan
Planning your response to incidents has two main advantages. Firstly, you won’t need to invent a plan of action in the heat of the moment and run the risk of forgetting something important. Without an incident response plan, your team’s reaction to any incident will likely be uncoordinated, slow, and incomplete. Secondly, you can plan for various scenarios and learn from actual incidents that occur, adjusting your plan to improve how you would respond in future.
Incident response plans aren’t limited to dealing with data loss, and not every data loss will need you to implement your incident response plan. But your company should have planned for responding to potential data breaches - incidents in which the response of your Salesforce team will be vital.
Incident response plans make clear who should do what during and after a serious incident. Not every incident needs the same people to respond; it depends on the scenario. For instance, data theft is even more problematic than accidental data deletion. Your incident response plan will nominate an incident commander whose first task is always to assemble and coordinate a team of the right people for any given incident. Subject to the scope of the incident, it may be that technical, legal, and communications teams all need to be involved. Your Salesforce team will own the technical response, but you’ll also need to support the other teams.
London, UK
Agentforce World Tour London
Supporting the communications team
Clear communication is key to managing any incident, and data loss is no exception. Internally, relevant teams and departments need to be informed and instructed. Externally, customers will want to know what data might have been compromised, and what they should do to protect themselves from further risk. It’s essential that concrete information is shared promptly, so as soon as you work out what data has been lost, accessed, or corrupted, pass this information to the incident commander. The communications team may help you with internal communications if, for example, you decide that it would be best for the sales team to stop adding new records to your org during the incident in case the new data also gets lost or compromised.
Supporting the legal response
Most breaches of personal data will need to be reported to the relevant data protection authorities. But the precise definition of personal data, the mechanisms for reporting, and the companies liable all vary between jurisdictions. Whoever is responsible for your company’s legal response should have found out in advance which data breaches your company is liable to report to which authorities. Once you have the complete picture of what happened during the data incident, that person will need this information to know what action they should take. As you investigate what went wrong, you should also try to preserve any evidence that may help to establish or prove what happened - and who was responsible.
Managing the technical response
Your main responsibility is the technical response. When it comes to data loss, it will very often be your team that first notices and reports the incident, prompting the implementation of the incident response plan. This is especially the case if you’re monitoring your org’s data and metadata with Gearset. Rushing to restore data as soon as you see data loss can exacerbate problems. Your incident response plan should guide you through the following common-sense steps:
- Identify the nature and cause of the data loss. What data has been affected by the breach? Has the personal information of customers or employees been compromised? Who’s responsible for the data breach? Are they internal or external to the company?
- Contain the data loss if it is ongoing. This might involve adjusting permissions metadata in order to revoke access to data. Or you might need to stop a batch Apex job that you realize is corrupting data.
- Eradicate the root cause of the data breach. For example, you’d deactivate a user identified as the culprit responsible for malicious deletions. Or you’d fix the faulty Apex job.
- Restore metadata and data from your backups, following a planned process.
- Learn the lessons once the incident is over. Could the breach have been prevented? If the same incident were to happen again, how could your response be better?
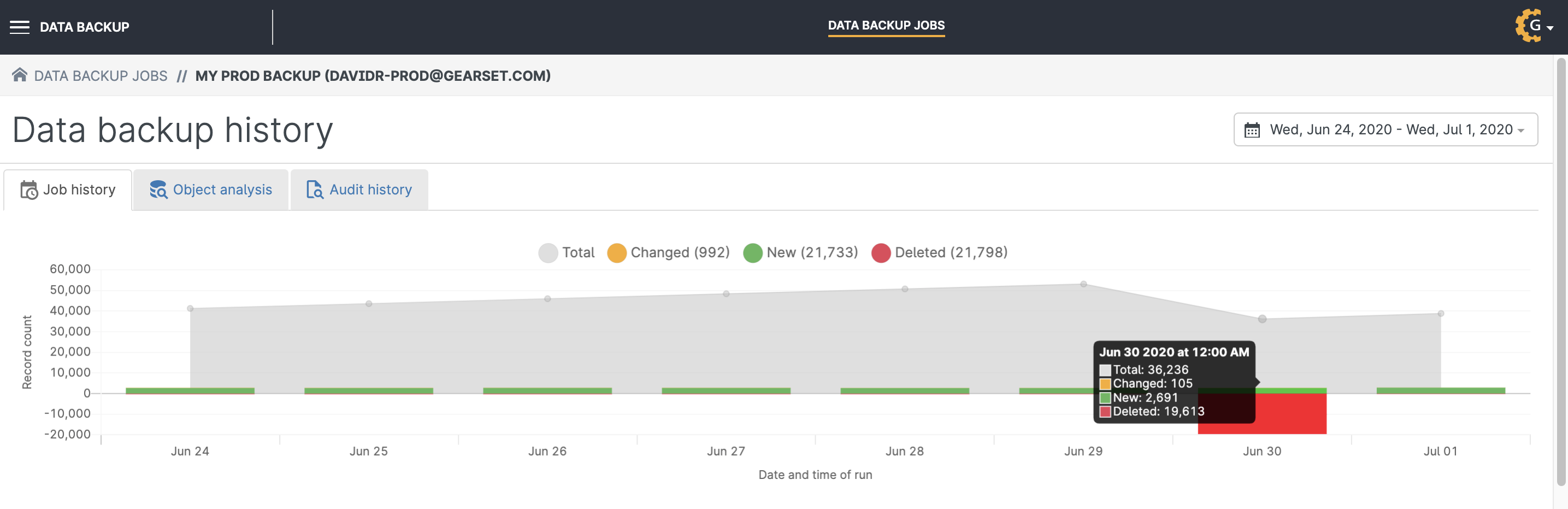
There are various ways in which Gearset’s backup solution can help you through these steps. To help identify the problem, you could set up Gearset’s smart alerts to warn you of data loss, and then use Gearset to work out exactly what’s missing or changed in your org. And you’ll be able to restore your org’s metadata and data reliably with Gearset, quickly getting your company back to operational normality.
Find out more about Gearset’s backup solution
If you’re putting together or revising an incident response plan, we hope you never have to use it! Sadly, data loss remains a risk for Salesforce orgs, so it’s important to be prepared. Gearset’s Salesforce backup solution will support your technical response to any data loss incident. You can see it in action in one of our tailored demos or if you want to learn more about how to secure your orgs, you can download our backup ebook.